Global domain name phishing email attack
 It has been brought to our attention that a domain name phishing email attempting to obtain sensitive information about our customers is masquerading as us – LiquidNet Ltd., as well as a number of other respected domain registrars, like eNom.
It has been brought to our attention that a domain name phishing email attempting to obtain sensitive information about our customers is masquerading as us – LiquidNet Ltd., as well as a number of other respected domain registrars, like eNom.
Phishing attacks like this are not something new. Nevertheless in this particular case the perpetrators have demonstrated a higher level of sophistication – by including a specific domain name that is owned by the given recipient, rather than some random content.
What is the domain name phishing email about?
Here is an example of the appearance of a phishing email:
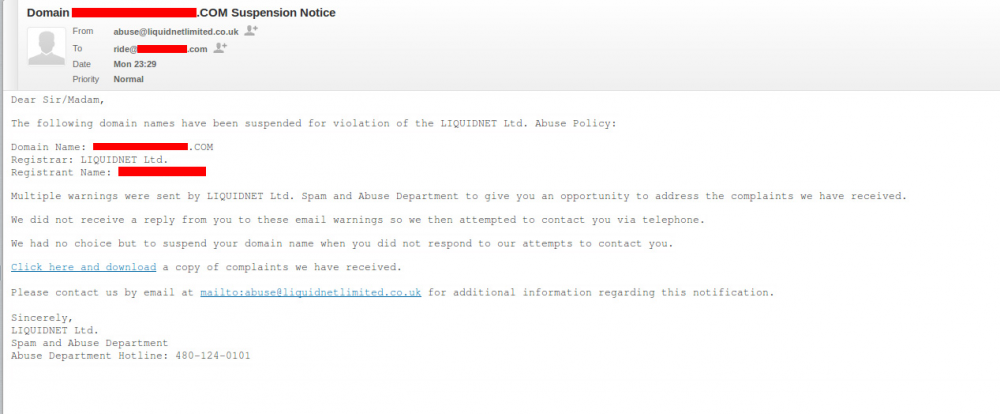
The accurate domain owner information along with the sense of urgency created by the phishers are among the primary factors that deceived so many of our users. The links in the email led to virus-infected websites.
We’ve since notified the companies hosting the phishing sites, and as a result the harmful pages have been suspended. It is possible that a number of infected pages may still be online – therefore remain cautious.
What should you do when you receive a domain name phishing email?
First and foremost:
DO NOT CLICK ON ANY OF THE LINKS IN THE EMAIL!
A very simple and quick way to verify whether the email sender is authentic is by hovering the mouse cursor over the link. This way you’ll be able to see where the link would be redirecting you to without actually clicking on it.
In phishing emails the sender’s address is always masked as a legitimate one. However, you’ll be able to easily recognize if the message has come from a notorious phishing location such as China.
A phishing email’s Return-Path header would look something like this:
Return-Path:
Received: from stu.xjtu.edu.cn
X-EQAUTHUSER: zhhliu@stu.xjtu.edu.cn
In order to see the full URL, smartphone users can press and hold the link.
In case you feel suspicious about a certain email – feel free to forward it to support@resellerspanel.com and we’ll reply as quickly as possible.

Leave a Reply