How to protect sites from CryptoPHP malware
 Some time ago, our admin team found out about a series of attacks on CMS-based websites on our platform. The attacks seemed to be part of the CryptoPHP hacker “campaign”.
Some time ago, our admin team found out about a series of attacks on CMS-based websites on our platform. The attacks seemed to be part of the CryptoPHP hacker “campaign”.
CryptoPHP compromises web servers by using backdoored plugins and themes for WordPress, Joomla and Drupal.
This widespread problem was first discovered by experts in the Netherlands when they came across a compromised Joomla plugin on one of their customers’ websites. The plugin originated from a legitimate-seeming website. On it one could find a rich selection of absolutely free, yet compromised, themes and plugins.
What is the CryptoPHP malware all about?
When users install pirated CMS plugins and themes – they also unknowingly install the CryptoPHP backdoor. Subsequently, the attackers use this backdoor to in order to gain control over the users’ websites.
Not only can the CryptoPHP malware inject infected content into the compromised websites, but it can also update itself.
Experts believe that the main reason why the CryptoPHP malware was created is to conduct blackhat SEO operations. Numerous analyses have shown that the compromised pages were injected with texts and links thus tricking crawlers into giving the hacker websites backlink credit and a pagerank.
By the most current estimations CryptoPHP has affected at least several thousand websites.
How are sites on our platform affected by CryptoPHP?
The CryptoPHP hackers managed to gain access to several CMS websites on our platform. When our team of experts completed their thorough examination of the affected sites, they concluded that all of them contained files such as ‘social.png’, ‘social0.png’, or ‘social1.png’ in their code, which are actually PHP scripts rather than PNG files.
Even though our team managed to remove the malware from the websites, they remain vulnerable – in case any of the owners decide to install another pirated CMS plugin or theme.
What should I do to make sure I am not affected?
You can be subjected to a CryptoPHP attack, in case you have ever installed pirated or untrusted WordPress/Joomla/Drupal plugins/themes/templates.
You ought to make it your first order of business to check your websites for files named ‘social.png’. Provided the file is a PHP script rather than a PNG file – you have been backdoored.
Since the backdoored websites are trying to make outgoing connections to certain IPs, as a temporary solution, you can activate the Outgoing Connections Firewall from your Web Hosting Control Panel:
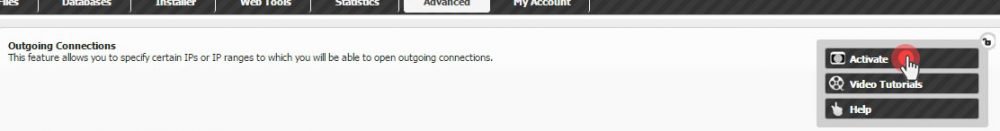
This way, you’ll be able to pause the attack until you find a way to resolve the problem.
If you want to download and use CMS themes/plugins – do it from the websites of trusted developers – that’s the one and only way to stay 100% safe.
Here is the entire report of the Dutch company which discovered the CryptoPHP malware: https://foxitsecurity.files.wordpress.com/2014/11/cryptophp-whitepaper-foxsrt-v4.pdf

Leave a Reply